Hotel and lodging industry must update best practices due to 2016 and 2017 changes in Visa and MasterCard rules. Cardholder authentication and multiple authorization indicators are two key components of change. Hotels that comply will maximize profits and security. Noncompliance will result in higher credit card acceptance fees due to penalties, increased declines, reduced profits, and new chargeback risk.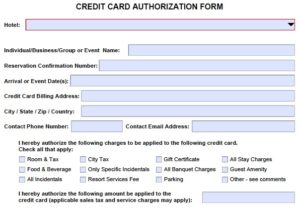 For those still using paper credit card authorization forms, few are in compliance with Visa Core Rules 5.4.2.5 Prohibition against Requiring Cardholder or Account Data – US Region.
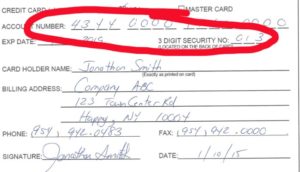
For those still using paper credit card authorization forms, few are in compliance with Visa Core Rules 5.4.2.5 Prohibition against Requiring Cardholder or Account Data – US Region.
“A US Merchant or its agent must not: Request the Card Verification Value 2 data on any paper Order Form.”
Authorization validity is front and center to the 2017 rules changes. Merchants used to get and authorization, and settle it later at checkout. Now merchants must send the correct transaction types and link them all together with a unique identifier:
- The ESTIMATE (Visa) or UNDEFINED (MasterCard) indicator is sent when the final settlement amount is unknown. The customer must be informed that it is an estimate as well.
- INCREMENTAL authorization is obtained when the original authorization expires or to increase the amount on hold.
- Final Authorization says this is the final transaction.
TIP: Merchants need 3-D Secure (Verified by Visa, MasterCard SecureCode), a global cardholder authentication standard for card absent transactions, to maximize profits and compliance for card not present transactions, which is only available with customer initiated transactions: hosted pay page, digital payment request, online booking. Paper forms don’t create a digital record tied to the credit card, and cardholder authentication is not possible, as defined by the card brands. It’s also not possible to comply with the rule by key entering data into any desktop terminal.
The unique transaction transaction identifier can be a point of breakdown in the process. For example, the events manager obtains a paper credit card authorization form. The first charge is a deposit; the second charge is at the end of the event; a third charge occurs after assessing damages to a room. In each case, the amount is key entered into the payment processing terminal. Since there is no transaction identifier tying them all together, the authorizations are invalid and the ISSUER is within their rights to chargeback for invalid authorization, example Visa reason code 72.
There are so many nuances to the rules, and changes needed in the payments ecosystem, hotels should not assume existing partners have completed the required updates to comply. Technology that can automatically manage the authorization and settlement process- not the old way, but with all the new rules changes- requires a sophisticated payment gateway. Like EMV, there will be vendors that struggle to adapt.
For compliant solutions that can be used standalone or integrated, improving your customer experience, contact Christine Speedy, 954-942-0483.
Reference materials:
- MasterCard® Pre & Final Authorization Mandate by CyberSource, December 2016.
- Visa Core Rules October 2016.
- MasterCard Revises Standards for Processing Authorizations and Preauthorizations by Vantiv December 2016.
- MasterCard Transaction Processing Rules, November 2016.
See merchant bulletins – downloads for links to many resources.