Are increasing merchant services credit card fees annoying you?
While technology can optimize fee management, there are multiple reasons new fees or rising fees may occur. Use the information for a quick self-assessment and determine whether it’s worthwhile to engage with a 3D Merchant Services payments professional for further review. This method is easier than my B2B credit card processing fact check, while still revealing problems that must be resolved. As a processor neutral payments expert, Christine Speedy offers a unique perspective.
The areas needing most attention are rate qualification and other fees.
Here’s a shortcut to determine if you have authorization problems, which directly impact credit card processing transaction fees. Why is this important? Because unless you fix the underlying problem, switching merchant accounts will only provide partial relief from escalating transaction fees like non-. If you have any of these items below on your merchant statement, there’s a problem that is causing unnecessary extra costs.
- Mastercard Transaction Processing Excellence Fee – Nominal Authorizations
- Misuse
- Integrity
- Compliance or Non-compliance
- Standard / STD (any)
- EIRF
- Data rate I
- Data Rate II or Data Rate 2
- Chargeback: FRAUD TRANS-NO CARDHOLDR AUTH
- Chargeback reason: Compliance
- Non-Qualified, NQ
Hint: If you open your merchant statement in Adobe Acrobat, in OSX with command F you can copy and paste the terms above. It’s not foolproof due to varying abbreviations, but you only need to have one of the bad items to know there’s a problem.
For card not present business to business, these are two credit card processing interchange types you should see; many often don’t and that is also a problems resulting in higher costs.
- Full UCAF
- Data Rate III, Commercial Level III
I don’t know why, but I get calls from other salespeople in the industry looking for solutions to help customers qualify for Data Rate II. Why wouldn’t you want the customer to qualify at Data Rate III? Makes no sense.
I also hear from merchants how they were told that the new solution would fix their level 3 data problems, but it didn’t. If you do preauthorizations, and the solution doesn’t automatically get new authorizations and manage reversals it’s not going to fix authorization problems. Always ask, “how will the payment gateway manage authorization reversals if we don’t settle for the original preauthorization amount’? That’s one of several critical key questions. If they don’t know the answer instantly, move on.
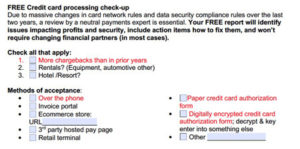
Due to constant changes in card network rules and data security compliance rules, a review by a neutral payments expert is essential. Did you have any red items? It’s time for a deeper dive into why. Your FREE report will identify issues impacting profits and security, include action items how to fix them, and rarely requires changing financial partners.
Call Christine Speedy, to reduce merchant fees with new or existing merchant account at 954-942-0483, 9-5 ET. With Christine as your account manager you’re assured a unique experience to maximize profits and security without business disruption.
3D Merchant Services is now WBE and WOSB certified and is rebranding to Greater Good Tech.