Distributors and manufacturers can overcome PCI Compliance issues with better awareness of rules, and cost efficient solutions to ease PCI burden. A review of key problems and solutions will help companies with internal credit card authorization and storage policies. For credit card processing, a virtual terminal or integrated gateway, is the only cost efficient and secure option for these business types.
It’s never Ok to store credit card forms that have the CVV2, or security code, on them. It’s also never Ok to store CVV2 electronically in any format, encrypted or not. This is both a card acceptance and PCI Compliance 3.0, section 3 Protect Cardholder Data, problem. For any recurring charges, including variable, merchants only need to validate the CVV one time for a fraud check, and then never again. This is easily accomplished with a zero dollar authorization, however not all gateways support this feature.
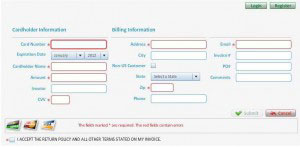
The best paper credit card authorization form, is one that doesn’t have full card data, or better yet, doesn’t exist at all. If sales reps in the field are getting card numbers to be charged later, consider a mobile payment app that let’s them swipe and create a token, using a P2P encrypted reader. That way card data is never exposed at any point in time. Instead of getting card numbers over the phone, empower customers to self pay or store card data using online payment solutions, including either a hosted online pay page or electronic bill presentment and payment (EBPP). Use this to also eliminate credit card data in emails, which is another PCI Compliance problem.
Need to keep a card stored on file that you initiate charges on? It’s indefensible with today’s technology to have credit card data on paper, and it’s risky to use your own encrypted media. Tokenization, a payment gateway service for merchants to remove sensitive data from their environments, is the best practice for security and PCI Compliance.
Some businesses want a signature on file. A sales receipt is generated with almost any online payment solution and merchants can require a customer to print and sign it, or to simply forward the email receipt from company email address with typed name approving it. For recurring billing, choose a payment gateway that generates a PCI Compliant recurring billing authorization form. They’re useless if stolen, and contain all the right language for credit card authorization. It should be supplemented by a signed document with your own custom business terms and conditions, and limitations for duration and maximum charge amounts allowed. Merchants might also get a signed sales order with all terms and conditions, plus the token ID the customer has agreed you’ll charge to.
Third-party credit card authorization doesn’t exist as far as card issuers are concerned. It’s specifically written in the cardholder terms that they cannot allow any third party to use their card. Any form a merchant creates authorizing other parties is at risk for future disputes. The merchant can eliminate the risk by having the company issue purchasing cards for each buyer, or mitigate risk by sending the sales receipt automatically to the cardholder and asking the buyer to confirm receipt per T’s & C’s.
A huge problem is managing old stored data created prior to new PCI Compliance rules. The reality is, the merchant is not PCI Compliant as long as the old stuff exists. That likely means someone will need to be assigned to identify all the past ways that credit card numbers were captured. For electronic, IT will need to get involved to securely remove old data. There are tools to search emails and servers for card data as well.
PCI 3.0, in effect now, requires merchants not only are PCI compliant at a point in time, but that there’s a plan in place for monitoring and inspecting. Whoever is cleaning up the old problems should document who, what, where, how and when activities were identified and or completed, and continually add this to the master PCI file.
References: