The best hotel third party authorization forms are fully compliant with card brand rules to mitigate chargeback risk, especially for friendly fraud, where cardholder claims they did not authorize the transaction. Fraud liability can be shifted nearly one hundred percent with best practices, plus risk of data breach from employee and other access to card data can be mitigated. Avoid the paper and digital credit card authorization form problems perpetuated by misinformation from people and incorrect internet postings.
Paper credit card authorization forms are dead.
Per Visa Core rule 5.4.2.5, October 2017, a US merchant or its agent must not Request the Card Verification Value 2 data on any paper Order Form. Update, in October 2018, the rule is now in section 5.4.3.1, Merchant Use of Account Number, Cardholder Signature, Card Verification Value 2 (CVV2), or Stored Credential. I could go on about all the PCI compliance and data breach risk problems related to credit card authorization forms, but because only 3-D secure cardholder authentication, which requires cardholder initiate payment, shifts friendly fraud liability for card not present transactions, there’s no valid reason not to change procedures. Get the cardholder data out of the hands of employees and networks. Secure document services where sensitive cardholder data can be viewed, or decrypted and viewed, for use in another solution are not PCI Compliant.
Web-based third party authorization forms are best for card absent compliance.
More than just PCI compliance, a myriad of rules changes since 2017, and continuing into 2019, impact every hotel. Everyone must change to comply and it’s not automatic. For example, you’re getting a sales deposit, and will definitely or will possibly charge more later. There’s a new set of transaction data standards which include estimate, incremental, and final authorization. While the technical piece is handled by payment gateways, not all have made the modifications required. Additionally, some elements are left to merchants to manage.
- Comply with Visa 5.8.3.1 Authorization Amount Requirements. The Merchant must use the Estimated/Initial Authorization Request indicator for the first transaction,
then the Incremental Authorization Request indicator for interim if applicable, and Final Authorization Request indicator when closing out the transaction; the same Transaction Identifier must be included for all Authorization Requests. Don’t accept an authorization online and then swipe or dip the same card later unless your card present system can tie back to the initial authorization.
- Stored cards. Are you storing cards for ongoing charges? Comply with Visa Rules Table 5-20: Requirements for Prepayments and Transactions Using Stored Credentials. There are too many variables to list here so I recommend downloading the rules and getting familiar. Two keys when capturing card data for the first time:
- Obtain express consent per specifications for your refund and cancellation policies, how you’ll use the stored card, when your agreement expires and how the Cardholder will be notified of any changes to the agreement.
- Perform a cardholder verification either via transaction or zero dollar authorization with the proper indicator.
- This is a change! Two transactions occur when capturing cardholder data for the first time. Again, technical part can be handled by a payment gateway that supports it, but other elements are left to you.
Hotel third party authorization form solutions.
Contact me for solution that works standalone or integrated with SynXis. Shift friendly fraud liability and potentially qualify transactions for better rates with your existing merchant account. That’s because non-compliance with various rules can result in higher fees.
Here’s some key elements if the initial authorization is not the final authorization. Terminology:
- PCI compliance- short for Payment Card Industry Data Security Standards. All businesses are mandated to comply with rules which are outlined on the PCI Security Standards Council web site.
- 3-D secure (3D Secure) is a global XML-based protocol designed to be an additional security layer for online credit and debit card transactions. Each card brand has their own version. For example, Verified by Visa. Merchants register for 3-D Secure with their acquirer; always consult with the payment gateway first for instructions and to confirm they’re registered to offer service. 3-D Secure is invoked automatically by the payment gateway which then based on issuer response may or may not prompt for additional information to authenticate the cardholder. Friendly fraud liability, “it wasn’t me, I didn’t authorize it”, shifts to the issuer. Because there are many parts to any transaction, including acquirer and issuer communications, plus continually changing rules, it’s possible that it will not be invoked.
- Link to Visa and all card brand Rules.
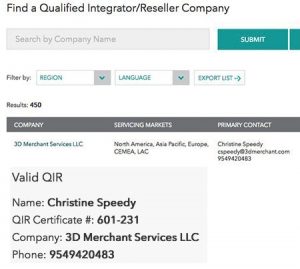
Call Christine Speedy, PCI Council QIR certified, for global sales. 954-942-0483, 9-5 ET, CenPOS authorized reseller based out of South Florida and NY. CenPOS is an integrated commerce technology platform driving innovative, omnichannel solutions tailored to meet a merchant’s market needs. Providing a single point of integration, the CenPOS platform combines payment, commerce and value-added functionality enabling merchants to transform their commerce experience, eliminate the need to manage complex integrations, reduce the burden of accepting payments and create deeper customer relationships.